
Bitcoin Developers Race to Build Quantum-Resistant Security: What It Means for Your Crypto
Bitcoin's official repository has received an updated proposal advocating for the freezing of wallets susceptible to quantum computing attacks.
Cybersecurity threats, protection strategies, and best practices

Bitcoin's official repository has received an updated proposal advocating for the freezing of wallets susceptible to quantum computing attacks.

Drum prüfe…Miljan Zivkovic | shutterstock.com Die wachsende Abhängigkeit von IT-Dienstleistern und Software von Drittanbietern vergrößert die Angriff...

Enterprise developers are racing to deploy AI agents in 2024 and 2025, but a fundamental problem is emerging: the security infrastructure wasn't built...

Three vulnerabilities demand immediate action from security teams in April's Patch Tuesday releases: a critical flaw in Windows Internet Key Exchan...

Security teams face a relentless operational reality: alert fatigue, accelerating threat actors, and mounting pressure to maintain uptime and resilience. For IT and security leaders, Managed Detection and Response (MDR) has emerged as a critical force multiplier—delivering the continuous monitoring, expert analysis, and rapid response capabilities that overwhelmed in-house teams struggle to sustain alone. By offloading detection and response functions to specialized providers, organizations gain 24/7 threat coverage without the overhead of scaling internal security operations. MDR bridges the gap between sophisticated threats and the finite capacity of modern security teams, enabling faster containment, reduced dwell time, and sharper focus on strategic priorities.

China-aligned threat actors are actively targeting multi-cloud environments with a Linux ELF backdoor engineered specifically to harvest cloud credentials at scale. The malware has been observed exfiltrating authentication data from workloads running across AWS, GCP, Azure, and Alibaba Cloud platforms, per findings from Breakglass Intelligence. The cross-platform targeting scope signals a deliberate strategy to compromise cloud-native infrastructure regardless of provider, making this a critical concern for security teams managing hybrid or multi-cloud deployments.
Hyundai Motor Group is evolving into a physical AI company, embedding artificial intelligence into robots and autonomous systems that interact with and respond to real-world environments. This strategic shift positions the automaker at the intersection of mobility, robotics, and embodied intelligence.

Artificial intelligence is fundamentally changing how security teams detect and hunt cyber threats. By analyzing massive volumes of security data,...
Artificial intelligence has transitioned from experimental technology to operational reality in cybersecurity. Security executives are no longer de...

Explore Chewy coupon codes for $30 off, $20 off your first order $49, 50% off pet food, and more April 2026 discounts.

The cybersecurity community is grappling with a fundamental shift in how vulnerabilities are discovered and exploited. Anthropic's Glasswing disclosur...

With almost ten years of hands-on testing, WIRED knows what separates the best fitness trackers from the rest.

The Marimo vulnerability represents a troubling milestone in the security of AI development tools: a critical flaw that went from public disclosure to...

Dale Hoak confronted a challenge that security leaders know well: identifying what falls outside their field of vision. As CISO at RegScale, Hoak ne...

# Federated Identity: Balancing User Convenience and Enterprise Security Federated Identity addresses one of enterprise security's most persistent tensions — user convenience versus robust access control — by enabling a single set of credentials to authenticate across multiple systems and organizational boundaries. Rather than maintaining siloed identity stores per application, federated models delegate authentication to a trusted Identity Provider (IdP), allowing seamless Single Sign-On (SSO) experiences across heterogeneous environments. Protocols such as SAML, OAuth 2.0, and OpenID Connect form the technical backbone of this architecture, standardizing how identity assertions are exchanged between parties. The core trade-off is complexity. While end users gain frictionless access and IT teams reduce password sprawl, organizations must invest in robust IdP infrastructure, rigorous trust relationship management, and carefully scoped token policies. A misconfigured federation trust or overprivileged token can propagate access risks across every connected system simultaneously — making the blast radius of a breach significantly larger than in isolated identity models. For enterprise architects, the value proposition is clear: federated identity reduces credential fatigue, centralizes access governance, and simplifies offboarding workflows. However, realizing these benefits requires mature identity hygiene practices, continuous monitoring of federation endpoints, and well-defined attribute mapping to prevent privilege escalation across domain boundaries. In short, Federated Identity delivers measurable gains in both usability and security — provided organizations are willing to absorb the upfront architectural complexity it demands.

Google has expanded Gmail's client-side encryption (CSE) support to Android and iOS, bringing end-to-end encryption capabilities to mobile users for the first time. The update ensures that encrypted email composition and reading can now happen natively on mobile platforms, closing a significant gap that previously limited CSE to desktop environments. For enterprise users and security-conscious organizations already leveraging Gmail's CSE framework, this extension to mobile broadens practical usability without compromising the encryption model where only the sender and recipient hold decryption keys — not Google.
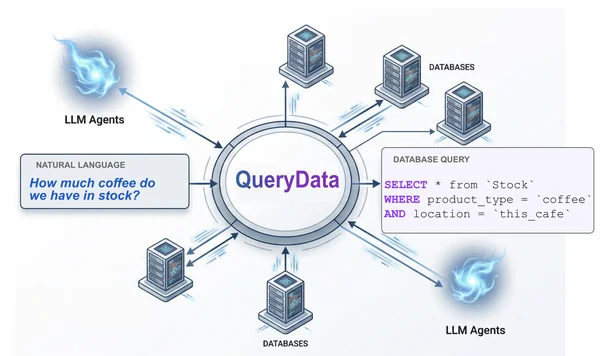
QueryData debuts in preview as a natural language-to-database query translation tool delivering near-perfect accuracy. The platform enables developers to create agentic experiences across AlloyDB and Cloud SQL databases, streamlining data access through conversational interfaces.
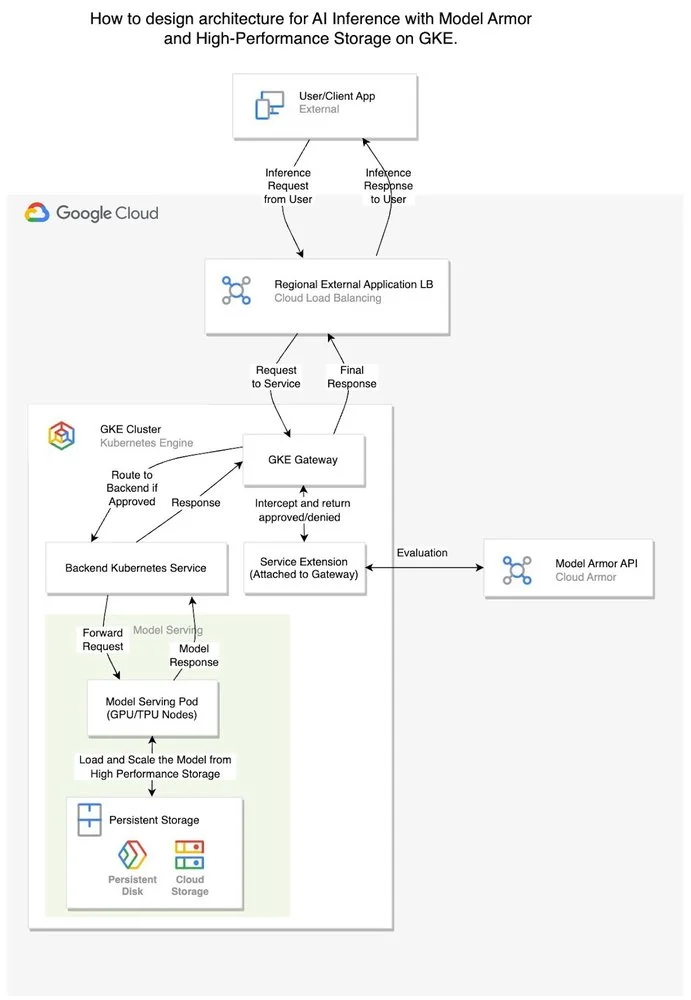
As enterprises scale AI workloads from proof-of-concept to production on Google Kubernetes Engine (GKE), they're discovering that traditional security...
LAB3 streamlines enterprise cloud operations by replacing fragmented ticket-based processes with an integrated workflow that spans infrastructure, security, and networking teams.

Do you need a pair of cheap earbuds? These JLabs are the ones.