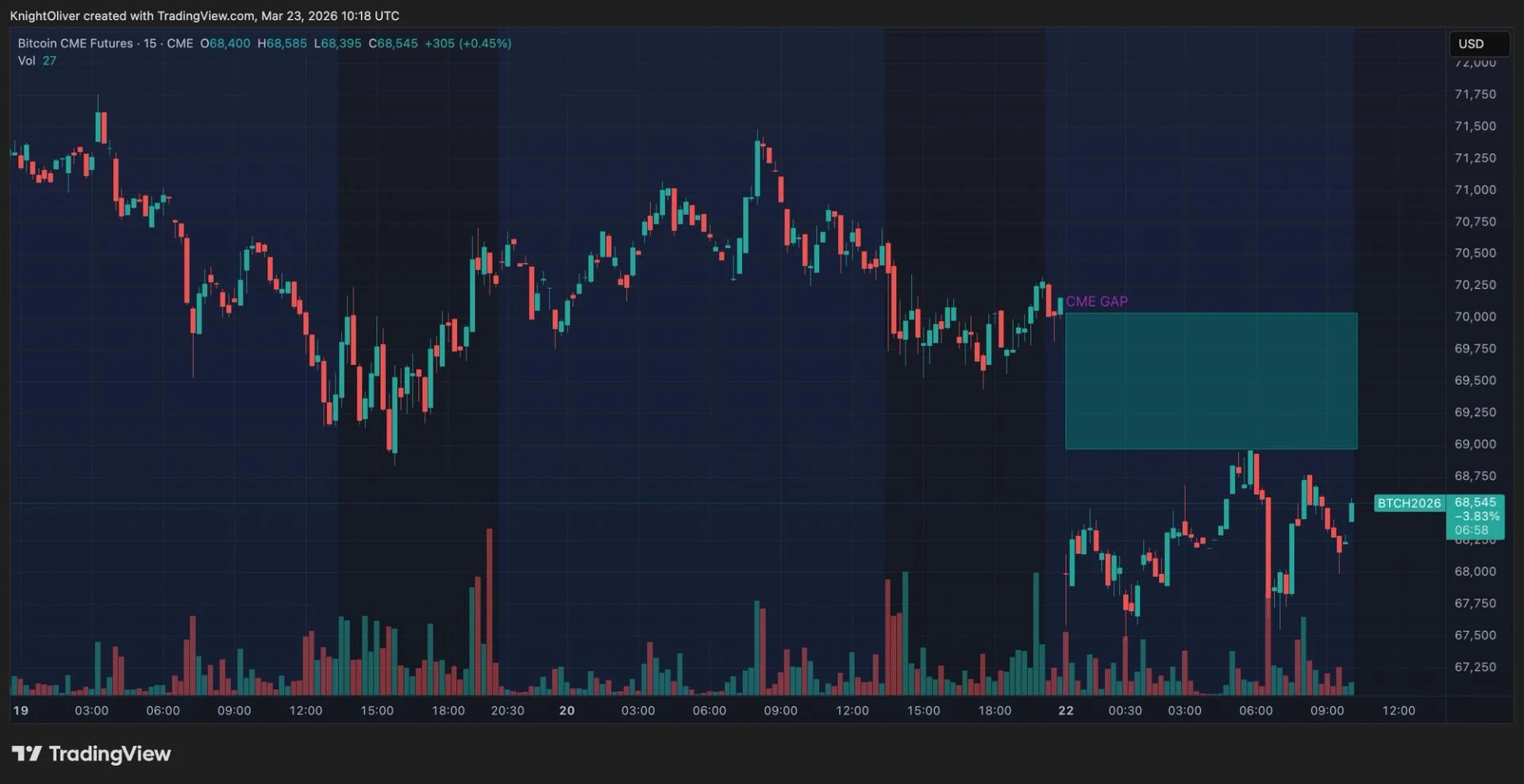
Bitcoin Pulls Back to $68,000: What the CME Gap Signals for a Potential $70,000 Recovery
Bitcoin retreated into its February trading range as geopolitical tensions flared — Trump's threats to strike Iranian power infrastructure triggered a broad risk-off move, rotating capital out of crypto and into commodity markets.