
What Is the Best Fitness Tracker in 2026? Garmin, Oura, More
With almost ten years of hands-on testing, WIRED knows what separates the best fitness trackers from the rest.
Data analysis, big data, and business intelligence

With almost ten years of hands-on testing, WIRED knows what separates the best fitness trackers from the rest.

Shingles causes persistent pain, elevates stroke risk, and inflicts permanent nerve damage in millions of patients, despite widely available preventive vaccines going underutilized.
Scientists racing against publication deadlines face a tempting proposition: AI coding agents that promise to write entire data analyses in minutes. B...
BYD's premium Denza Z9 GT demonstrated a 9-minute battery charge in WIRED's testing, showcasing breakthrough charging speed. However, the brand's pricing strategy appears misaligned with market positioning.

The Marimo vulnerability represents a troubling milestone in the security of AI development tools: a critical flaw that went from public disclosure to...

Water filters promise the moon—but only some back up their claims. Here are the best filtered-water pitchers for those who prefer their water free of heavy metals and forever chemicals.

Journalists and advocacy organizations are mobilizing to defend the Internet Archive's extensive web page repository as prominent news publishers block Wayback Machine access to their content.
Pixel Societies leverages AI agents to model social dynamics, aiming to streamline how users evaluate potential colleagues, friends, and romantic connections through simulated interactions.
Many companies are taking a slower, more controlled approach to autonomous systems as AI adoption grows. Rather than deploying systems that act on their own, they are focusing on tools that assist hum...

Dale Hoak confronted a challenge that security leaders know well: identifying what falls outside their field of vision. As CISO at RegScale, Hoak ne...

# Federated Identity: Balancing User Convenience and Enterprise Security Federated Identity addresses one of enterprise security's most persistent tensions — user convenience versus robust access control — by enabling a single set of credentials to authenticate across multiple systems and organizational boundaries. Rather than maintaining siloed identity stores per application, federated models delegate authentication to a trusted Identity Provider (IdP), allowing seamless Single Sign-On (SSO) experiences across heterogeneous environments. Protocols such as SAML, OAuth 2.0, and OpenID Connect form the technical backbone of this architecture, standardizing how identity assertions are exchanged between parties. The core trade-off is complexity. While end users gain frictionless access and IT teams reduce password sprawl, organizations must invest in robust IdP infrastructure, rigorous trust relationship management, and carefully scoped token policies. A misconfigured federation trust or overprivileged token can propagate access risks across every connected system simultaneously — making the blast radius of a breach significantly larger than in isolated identity models. For enterprise architects, the value proposition is clear: federated identity reduces credential fatigue, centralizes access governance, and simplifies offboarding workflows. However, realizing these benefits requires mature identity hygiene practices, continuous monitoring of federation endpoints, and well-defined attribute mapping to prevent privilege escalation across domain boundaries. In short, Federated Identity delivers measurable gains in both usability and security — provided organizations are willing to absorb the upfront architectural complexity it demands.
[This article was first published on rOpenSci - open tools for open science, and kindly contributed to R-bloggers]. (You can report issue about the...
**Rethink A/B Test Sizing: Optimize for Profit Over Statistical Purity** Traditional A/B test sizing focuses on statistical significance, but finite campaigns demand a different approach. When resources are limited, testing becomes a strategic trade-off between learning and earning. Instead of designing tests solely for perfect inference, balance sample allocation against opportunity cost. Prioritize tests that maximize expected profit within your constraints, recognizing that smaller, faster experiments often deliver better business outcomes than statistically ideal but resource-intensive designs.
[This article was first published on T. Moudiki's Webpage - R, and kindly contributed to R-bloggers]. (You can report issues about the content on thi...
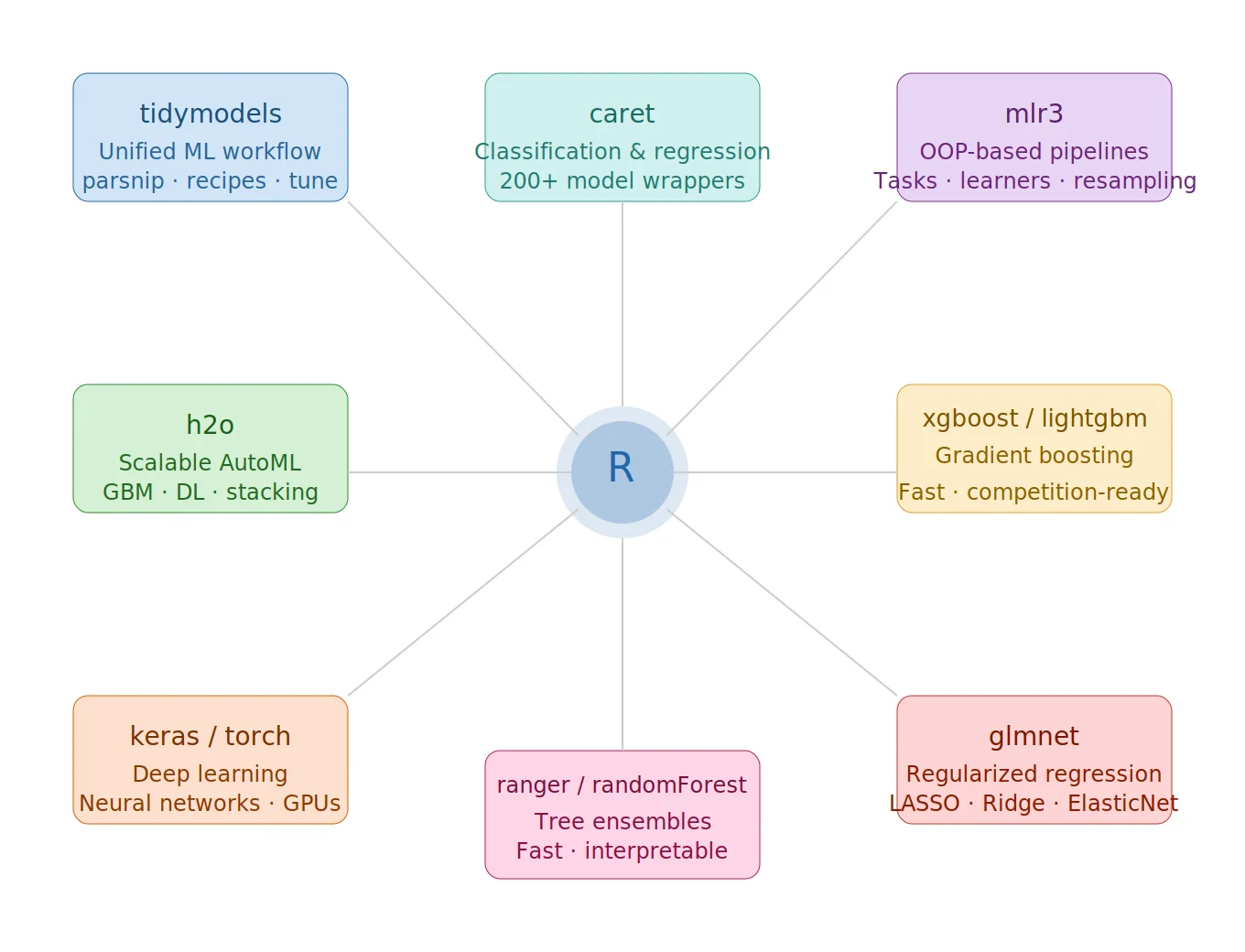
R’s ecosystem offers a rich selection of machine learning frameworks, each with distinct design philosophies and strengths. This post is a side-by-side comparison of five ML frameworks in R that provi...

Google has expanded Gmail's client-side encryption (CSE) support to Android and iOS, bringing end-to-end encryption capabilities to mobile users for the first time. The update ensures that encrypted email composition and reading can now happen natively on mobile platforms, closing a significant gap that previously limited CSE to desktop environments. For enterprise users and security-conscious organizations already leveraging Gmail's CSE framework, this extension to mobile broadens practical usability without compromising the encryption model where only the sender and recipient hold decryption keys — not Google.
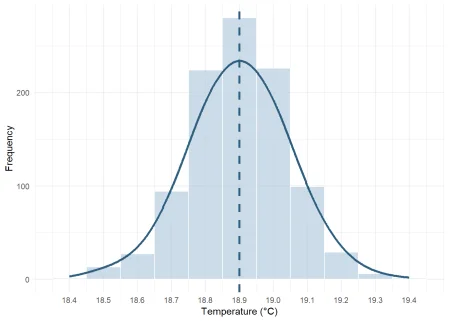
CRAN, GitHub TL;DR: {bdlnm} brings Bayesian Distributed Lag Non-Linear Models (B-DLNMs) to R using INLA, allowing to model complex DLNMs, quantify uncertainty, and produce rich visualizations. Backgro...
Enterprise data typically lives scattered across dozens of source systems. Data curation—the work of organizing, cleaning, and enriching raw informat...
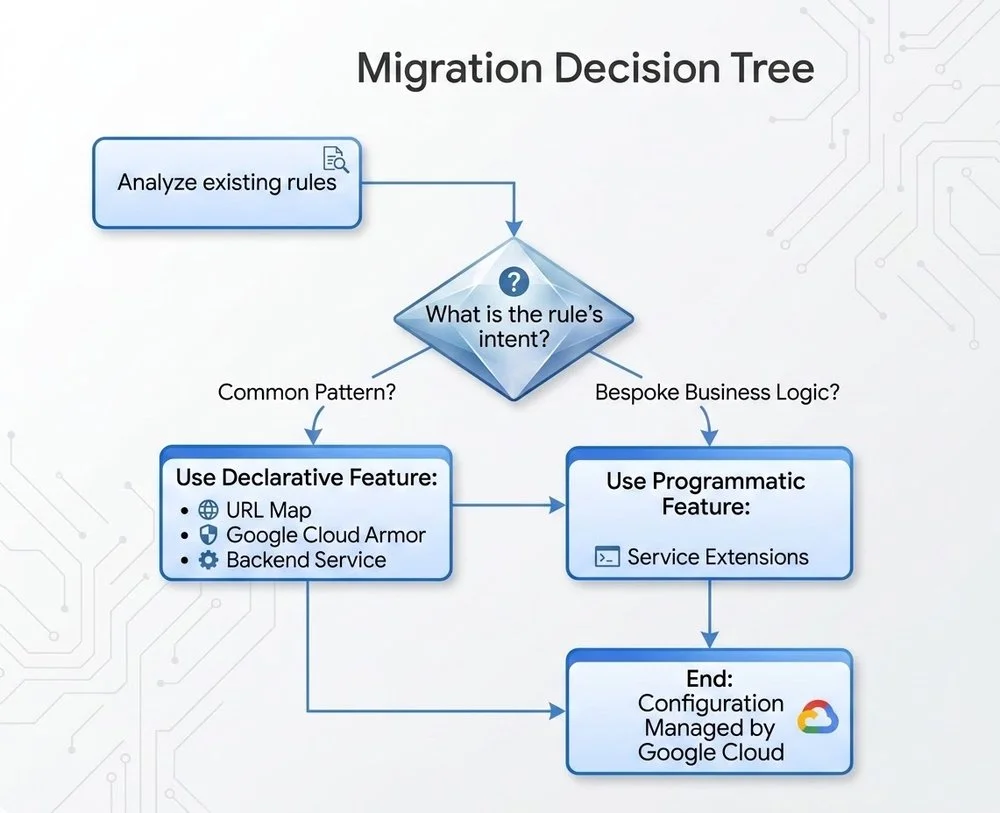
Transitioning application load balancer infrastructure from on-premises hardware to Cloud Load Balancing unlocks meaningful gains in scalability, cost efficiency, and native cloud integration. Unlike static hardware deployments, cloud-native load balancing dynamically distributes traffic across backend services, automatically scaling capacity to match demand without manual intervention. Organizations eliminate the capital expenditure and maintenance overhead tied to physical appliances, shifting to a consumption-based model that aligns costs directly with usage. Deep integration with cloud-native services—including managed health checks, SSL termination, and global anycast networking—reduces operational complexity while improving availability. Teams gain centralized visibility through unified logging and monitoring, accelerating troubleshooting and performance optimization across distributed architectures.
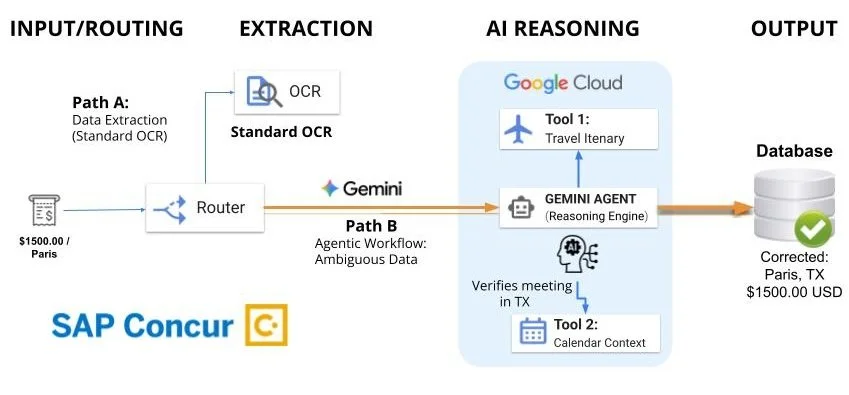
Expense automation has long operated on a straightforward principle: machines that can read text can handle the processing. Yet anyone who's submitted...